Copyright Information
Important Links
- The Digital Millennium Copyright Act of 1998 (PDF)
- Copyright: What Makes a Use "Fair"?
- Troy University Copyright Policy
- Electronic Copyrights Infringements Policy
Section 1 - Copyright Information
- 1-1. Link to relevant Web page(s)
IT copyright best practices page, http://it.troy.edu/policies/copyright/
- 1-2. What technology-based deterrent(s) have you decided to use?
We are using our firewall's application content filtering capabilities to block peer-to-peer application activity. We are also using bandwidth shaping to throttle general HTTP traffic.
- 1-3. What mechanism(s) are you using to educate your community?
Beginning of each semester sending "Information Security Best Practices" e-mail to all students, faculty and staff with information and URL. Scheduling speaking engagements to "Freshmen Orientation" events. Quarterly IT newsletter includes security and copyright tips.
- 1-4. What procedures are you using for handling unauthorized distribution of copyrighted material (e.g., monitoring, sanctions, etc.)?
Investigate instances that we discover either by TROY abuse tickets, DMCA notices, through network traffic discovery (high bandwidth) or student's network storage drive (music/movie files) discovery. Notification of students by Resnet department via e-mail of infraction and the incident will be turned over to the Dean of Students Office for a judgment hearing.
- 1-5. How are you periodically reviewing the plan? What criteria are you using to determine if it is effectively combating copyright infringement?
By monitoring the amount of TROY copyright infringement abuse tickets, DMCA notices received and internal incidents. Student feedback from information security communications.
Section 2 - Offering Alternatives
- 2-1. Link to relevant Web page(s)
Library Copyright Guides and Resources
The Digital Millennium Copyright Act of 1998 (DMCA) (PDF)
MPAA Letter to College & University Presidents (PDF)
Legal Alternatives to Downloading Copyrighted Material
- 2-2. Are you carrying out your own survey of alternatives or linking to one or more lists maintained by others? If the latter, which list(s)?
See above.
- 2-3. Have you made any special arrangements with one or more content providers to obtain content through legal methods?
No; using the alternatives provided. Paid content services, such as iTunes are not blocked.
Section 3 - Informing the Community
- 3-1. Link to relevant Web page(s)
Troy University IT Copyright webpage, http://it.troy.edu/policies/copyright/
- 3-2. Have you developed your own statement regarding copyright and copyright law in general or are you linking to such statement(s) maintained by others? If the latter, which statement(s)?
From TROY Student Handbook, Oracle. Policies and Procedures section, IT Policy and Resnet Policy. Also, Student Academic code from the Oracle:
Academic Code
A student is subject to disciplinary action if:
- In connection with a student's admission, readmission, enrollment, or status in the university:
- A student gives false information to the university concerning any matter which may properly be considered in that connection; or
- A student knowingly withholds from the University any information requested by the University.
- In connection with the taking of, or in contemplation of the taking of any examination by any person:
- A student knowingly discovers or attempts to discover the contents of an examination before the contents are revealed by the instructor;
- A student obtains, uses, attempts to obtain or use, or supplies or attempts to supply to any person, any unauthorized material or device;
- A student uses, attempts to use, or supplies or attempts to supply to any person any material or device dishonestly.
- Where the work affects or might affect a student's grade, credit, or status in the university, a student represents to be his or her own any work that is not the product of his or her own study and efforts (known as plagiarism).Also reference the U.S. Copyright Office.
- In connection with a student's admission, readmission, enrollment, or status in the university:
Section 4 - Use of Streaming Video in the Classroom
- 4-1. Can I show Netflix, Hulu, Amazon Prime, etc videos in my classroom?
There may be times when a faculty member wishes to show a film or documentary in class that is housed on a 3rd party streaming site like Netflix, Hulu, or Amazon Prime. As 3rd party sites offer more original/exclusive content, the terms and conditions of fair use blur. This information will serve as a starting point to understanding usage restrictions in an effort to comply with copyright laws and licensing terms.
Keep in mind that 3rd party streaming account licenses overrule copyright exemptions. For example, showing your personal DVD during class is covered by a specific copyright exemption (Section 110), and showing clips can be covered by fair use (Section 107). However, streaming videos from personal subscription vendors in your classroom when the license prohibits such viewings - there is no copyright exemption for that, leading to a problematic situation.
Also note - Troy University does not obtain institutional accounts with the 3rd party streaming services listed below.
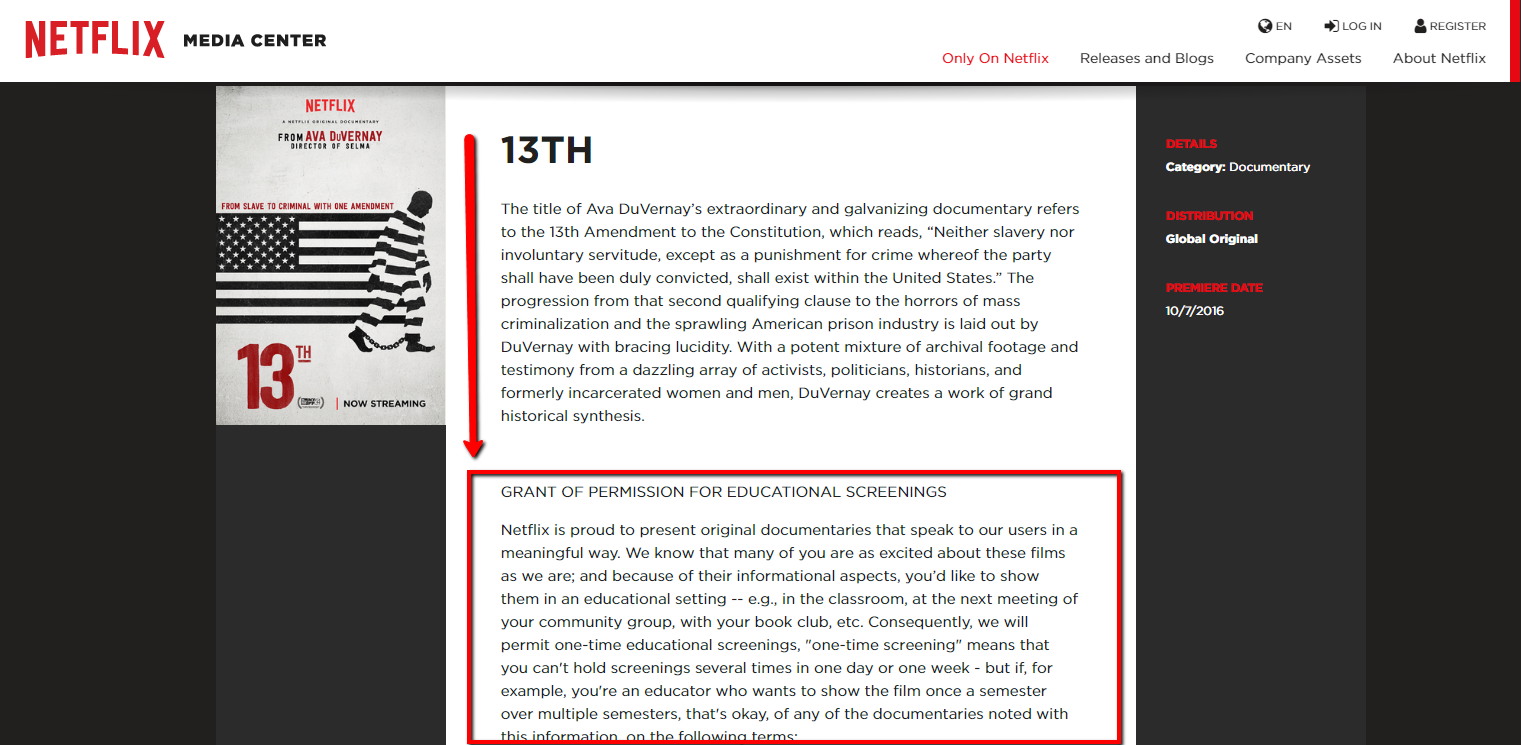
Netflix
Netflix has made provisions for educational use of "select"Netflix Original Documentaries. This does not include the entire Netflix database. Additionally, when agreeing to Netflix Terms and Conditions upon account creation, specifications state that the "service and any content viewed through the service is for your personal and non-commercial use only."
The instructions below should be used with your personal account information. To determine if a documentary you wish to stream in a classroom setting is included, complete the following steps:- Navigate to this "All Alphabetical" listing page.
- Locate and click the title of the film/documentary you wish to view from the list.
- If an educational screening Grant of Permission is included, you will see it stated on the description page for the film.
- The Grant of Permission entitles a one-time educational screening of permitted documentaries.
- You cannot hold screenings of the same documentary several times in one day or one week or one semester.
- You can show a documentary once a semester over multiple semesters.
- Hulu
When agreeing to Hulu Terms and Conditions upon account creation, specifications state that "using the services, including accessing and viewing the Content on a streaming-only basis, [is for] personal, non-commercial purposes."
Hulu has not made provisions for educational screenings of its content. While classroom use would be non-commercial, it would not be considered personal use. Streaming Hulu content in a classroom setting would be a direct violation of licensing terms (section 3.2).
Amazon Prime
When agreeing to Amazon Prime Video Terms and Conditions upon account creation, specifications state that "Amazon grants you a non-exclusive, non-transferable, non-sublicensable, limited license, during the applicable Viewing Period, to access and view the Digital Content in accordance with the Usage Rules, for personal, non-commercial, private use."
Amazon has not made provisions for educational screenings of its content. While classroom use would be non-commercial, it would not be considered personal/private use. Streaming Amazon content in a classroom setting would be a direct violation of licensing terms (section 4h).
I Teach a Film Class. What Options Do I Have?
Streaming in a classroom setting from a service deemed for personal use violates the terms and conditions that ultimately trump any copyright exemptions. Options, while not ideal, could include:-
- Utilizing the Netflix Grant of Permission documentary titles as much as possible if streaming is necessary
- If a film is not included in the Grant of Permission list, requiring students to access film content on their own through their own personal subscription could be included in your syllabus as a course requirement. This would shift watch time to out of class, leaving discussions for in class - a flipped classroom approach.
- Purchasing DVD or Blue Ray disc when available.
- Contacting the streaming service directly could prove helpful to state your case. In researching this topic, Netflix seems to be the most helpful in providing verbal agreements in some cases to approve streaming in classroom settings. Keep in mind, there usually is no written agreement, and the answer given would be dependent upon who you speak with on any given day. Documentation of some sort would need to be kept by the faculty member.

